LazySysAdmin is a vulnerable machine available on VulnHub.com. It’s a relatively easy machine, and shouldn’t prove to be too hard for most beginner-intermediate people.
Enumerating LazySysAdmin
I began enumeration with a simple nmap scan. The Red Team Field Manual is a great reference for tools like nmap.
nmap 192.168.56.100
Starting Nmap 7.60 ( https://nmap.org ) at 2017-12-15 15:45 CST
Nmap scan report for 192.168.56.100
Host is up (0.00026s latency).
Not shown: 994 closed ports
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
139/tcp open netbios-ssn
445/tcp open microsoft-ds
3306/tcp open mysql
6667/tcp open irc
MAC Address: 08:00:27:FC:E3:96 (Oracle VirtualBox virtual NIC)
Nmap done: 1 IP address (1 host up) scanned in 1.85 seconds
Since web-servers are usually a good place to find low-hanging fruit, I did a little further enumeration with dirb(excerpt):
GENERATED WORDS: 4612
---- Scanning URL: http://192.168.56.100/ ----
==> DIRECTORY: http://192.168.56.100/apache/
+ http://192.168.56.100/index.html (CODE:200|SIZE:36072)
+ http://192.168.56.100/info.php (CODE:200|SIZE:77272)
==> DIRECTORY: http://192.168.56.100/javascript/
==> DIRECTORY: http://192.168.56.100/old/
==> DIRECTORY: http://192.168.56.100/phpmyadmin/
+ http://192.168.56.100/robots.txt (CODE:200|SIZE:92)
+ http://192.168.56.100/server-status (CODE:403|SIZE:294)
==> DIRECTORY: http://192.168.56.100/test/
==> DIRECTORY: http://192.168.56.100/wordpress/
==> DIRECTORY: http://192.168.56.100/wp/ I poked around the various files/folders and didn’t find anything too useful. However, I did find a WordPress install in the /wordpress/ directory. WordPress is always a great avenue when it comes to server exploitation.
After enumerating the WordPress install, I didn’t find any obvious vulnerabilities or misconfigurations. At this point, I decided to run enum4linux and found a share I could mount:
Sharename Type Comment
--------- ---- -------
print$ Disk Printer Drivers
share$ Disk Sumshare
IPC$ IPC IPC Service (Web server)
Server Comment
--------- -------
Workgroup Master
--------- -------
WORKGROUP PAD-THAI
[+] Attempting to map shares on 192.168.56.100
//192.168.56.100/print$ Mapping: DENIED, Listing: N/A
//192.168.56.100/share$ Mapping: OK, Listing: OK
//192.168.56.100/IPC$ Mapping: OK Listing: DENIED
======================================================
| Password Policy Information for 192.168.56.100 |
======================================================
[E] Unexpected error from polenum:
Traceback (most recent call last):
File "/usr/bin/polenum", line 33, in
from impacket.dcerpc import dcerpc_v4, dcerpc, transport, samr
ImportError: cannot import name dcerpc_v4
[+] Retieved partial password policy with rpcclient:
Password Complexity: Disabled
Minimum Password Length: 5
Once mounted, I saw that I had read-only access to LazySysAdmin’s web root.
This allowed me to take a look at the wp-config.php file and get the database credentials:
/** MySQL database username */
define('DB_USER', 'Admin');
/** MySQL database password */
define('DB_PASSWORD', 'TogieMYSQL12345^^')
Armed with these credentials, I logged in to PHPMyAdmin, but couldn’t do too much. On a whim, I decided to try using the credentials to log into WordPress itself. The credentials worked, and I now had Admin access to WordPress.
For fun, I decided to add another Admin account named “pwned”:
Exploitation
With an Administrator account on wordpress, I was able to inject a PHP shell into the 404.php file. You can find this PHP shell on PentestMonkey.net. I’ve found this particular PHP shell to work reliably on multiple vulnerable machines now.
With the shell injected into the 404.php file, all I had to do was set up a listener on my machine and then trigger a 404 error on the wordpress site:
This resulted in a shell with www-data privileges on my machine:
Getting Root on LazySysAdmin
With a low-privilege shell, I now needed to escalate to root privileges in order to find/open the flag.
I like to use this linux privilege-escalation cheat sheet by g0tmi1k, which helps with system enumeration. After a while, I was drawing a blank. I didn’t find anything too interesting and GCC didn’t seem to be installed, which would make it difficult/impossible to compile an exploit on the server itself.
I decided to go back to the basics. Earlier, when looking through the smb share, I found a very basic password of “12345” in a file called deets.txt. I figured out that this was the password for the user “togie” on the server and was able to log in:
From there, it was just a matter of using “sudo su” to get root privileges:
Flag Found!
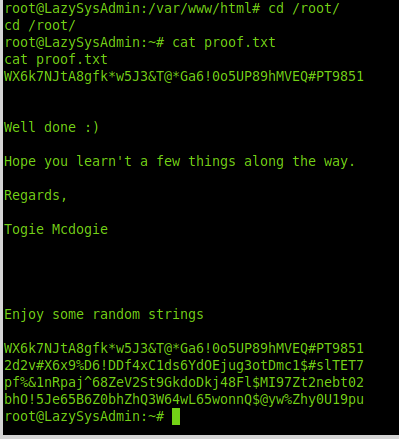
I navigated over to the /root/ folder and found the proof.txt file:
root@LazySysAdmin:~# ls
ls
proof.txt
root@LazySysAdmin:~# cat proof.txt
cat proof.txt
WX6k7NJtA8gfk*w5J3&T@*Ga6!0o5UP89hMVEQ#PT9851
Well done :)
Hope you learn't a few things along the way.
Regards,
Togie Mcdogie
Enjoy some random strings
WX6k7NJtA8gfk*w5J3&T@*Ga6!0o5UP89hMVEQ#PT9851
2d2v#X6x9%D6!DDf4xC1ds6YdOEjug3otDmc1$#slTET7
pf%&1nRpaj^68ZeV2St9GkdoDkj48Fl$MI97Zt2nebt02
bhO!5Je65B6Z0bhZhQ3W64wL65wonnQ$@yw%Zhy0U19pu
root@LazySysAdmin:~# Conclusion
This was a fun machine made possible by a truly LazySysAdmin. It really shows the importance of complete enumeration, as well as trying the basics before throwing more advanced exploits at a machine.
-Dave